Performing CyberOps Using Core Security Technologies (CBRCOR) Practice Tests and PDFs
Comprehensive preparation materials designed by certification experts
100% Certified
Weekly Update
100% Success
Performing CyberOps Using Core Security Technologies (CBRCOR)
Exam Code:
350-201
Vendor Name:
Cisco
Total Questions:
139
Last Updated Date:
March 9, 2025
Formate:
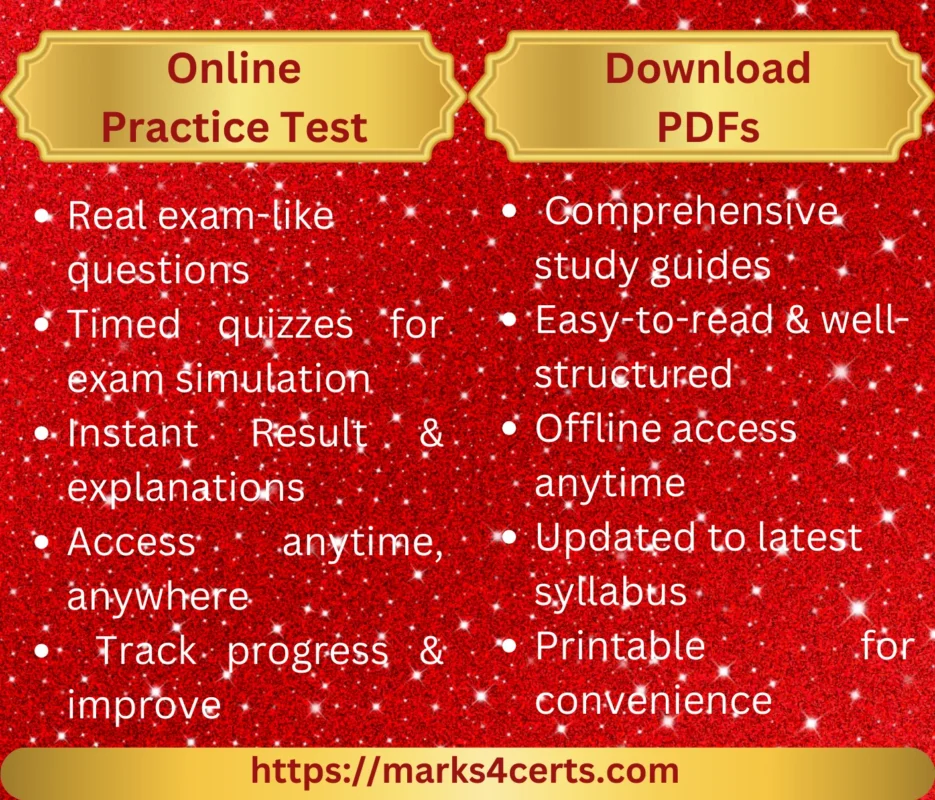
Practice Test Online
Downlaodable PDFs
Realistic Exam Simulation
Experience the actual exam environment before test day
Real exam-like questions
Questions mirror the actual certification exam format and difficulty
Price:
$49.00
350-201 Test Features
Passing 350-201 certification exams requires a significant amount of preparation. Proper study techniques and using the right resources can help you retain important information, understand key concepts, and ultimately pass the 350-201 exam. Different methods are available to help candidates prepare effectively. Our practice tests simulate the 350-201 actual exam environment, allowing candidates to experience the format, timing, and types of questions they will encounter. Taking multiple 350-201 practice tests can improve time management skills and help you identify areas that need further review.